In this two-part post, I look at why, if you have adopted Microsoft’s cloud, then you best adapt your security model. Part two will be available soon.
Have you adopted the Microsoft cloud? Has Microsoft 365 become a big part of the way your business operates? The answer in 1000’s of cases is yes and that number is only accelerating. There are lots of good reasons this has happened, flexibility, simplicity, scale, innovation, accessibility all of which deliver real business value.
I’ve worked with many businesses that have embraced what Microsoft 365 offers, changing how they operate and opening new paths for innovation. However, there is a “but”. The adoption of Microsoft 365 (and other cloud services) has not only changed the way we can operate it has also made our traditional security approaches, if not redundant, far less effective. We can no longer rely on the safety of the enterprise network with its perimeter firewalls and “locked-down” desktops, these models just do not work in a world where we have adopted the cloud.
Our infrastructure is more fragmented, our workforce equally so. If your security model still focuses on perimeters and hardened devices as ways of protecting your business, then it is time for a rethink. Ask yourself, where is your security perimeter today? The head office? The datacenter? A home office? Kitchen? bedroom? What exactly is your enterprise network? The consumer broadband at the chief execs home? Wi-fi in the local coffee shop? A mobile providers data network? And what are your enterprise devices? A heavily locked down desktop in the office? A laptop? An iPad that the kids play games on? The latest smartphone? Today all of these things are part of enterprise IT and these changes demand we rethink our security models.
The new threat
Why a rethink? Because these changes mean the threats to our business have changed. Why would a cybercriminal attack the head office if nobody is there? Or our data lives in the cloud? But if our data lives in Microsoft 365, the cybercriminal also knows trying to “hack” their way past Microsoft’s security boundaries is likely to be a thankless and near-impossible task, meaning their approach has had to change. A big part of this change is that identities are now at the forefront of the security threat. It makes perfect sense, because trying to “break in” to corporate IT is hard, it is time-consuming and expensive for the average cyber bad actor. However, acquire credentials that allow me to “stroll” past that same security, the job is much easier. That is why we have seen such a rise in phishing attacks. Because cyber criminals know many of us are still working with old security mechanisms, ones that mean the right credentials will be trusted implicitly, so the wrong person with the right credentials will have whatever freedoms those credentials allow.
Taking a Zero Trust approach
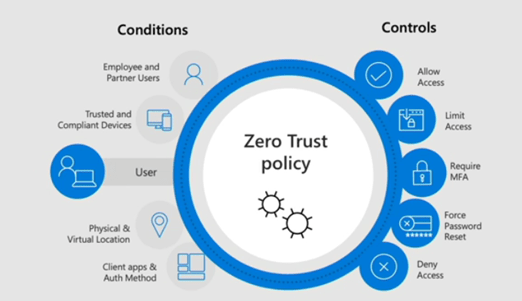
Zero trust is a strategic shift that addresses this fundamental new challenge. It does not rely on any single thing, be that trusted networks, secure perimeters or identity. Instead, a zero trust approach starts from a basis of assuming breach, rather than trusting anyone it trusts no one, it assumes we are all bad actors until convinced otherwise. Zero Trust needs to verify explicitly and even then, only offers least privileged access, constantly monitoring and analysing behaviour, warning or even automating responses to potentially risky or threatening activity. To be effective a Zero Trust approach relies on applying context to the way our resources are being used and it is this context that is crucial to addressing the new and complex security threats the modern business faces.
With all that in mind you may be asking yourself “was it a mistake to adopt Microsoft 365?” Absolutely not, because while adopting cloud presents new threats, importantly those same cloud providers are offering sophisticated solutions to tackling them. Solutions that traditionally have been out of reach for most, but because of the very nature of the cloud, are now easier to adopt than ever before.
Don’t worry, not only can you enjoy the benefits that your cloud adoption has provided, you can do so while making your business even more secure than it was when your technology was in your datacentre.
In part two of this post, I’ll share four technology pillars that Microsoft provides to help you secure your business. You can not find part two here.
One thought on “Adopted the Microsoft Cloud? Then better adapt your security model”