Recently I noticed the results of a survey carried out by security detection and response specialists SecureWorks that asked the following question.
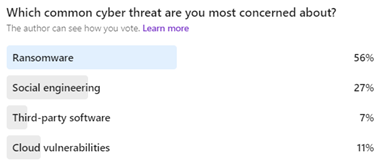
While seeing ransomware top of the list of concerns was no surprise, the results of this poll did get me thinking.
While ransomware is the headline grabber if we look into the other threat areas included in the responses they are all linked. Each is a vector that a cyber threat actor can use to deploy the malware necessary to trigger a ransomware attack.
It was this link that caught my attention. As we look to combat the security threat and impact of ransomware it is important to realise that it is the culmination of exploited risks in other layers of our security. Therefore to deal with it we need to take a multi-layered approach (I recently discussed this with Veeam’s Edwin Weijdema in this podcast).
So, while ransomware is a real risk, it can only impact us if it gains access to our systems and data. That is why those other areas are important to understand. Let’s look at how they are linked to the ransomware threat.
Social Engineering
While hacking the way through your security defences makes a better movie, it is hard. However, getting hold of your login credentials makes life much easier for our cyber-criminal.
Phishing attacks are the primary social engineering route. Carefully crafted emails and fake websites amongst others can all help to build a version of your digital identity and give an attacker access to an account to either steal data or in the case of ransomware, unleash a malicious payload.
Third-party software and Cloud vulnerabilities
Software vulnerabilities is a constant issue for the enterprise and the advice to patch regularly remains important. However, this threat has also evolved, not only with cloud adoption but also with a change in tack from cybercriminals. Two high profile recent attacks on SolarWinds and Kaseya highlight this. In both cases malicious code was injected into broadly used software, then rolled out as part of the software supply chain, introducing vulnerabilities to multiple customers simultaneously.
What does this all mean?
Hopefully, none of this is news to anyone reading this post. The cybersecurity threat is and continues to be a high-profile issue. It is multi-layered and while ransomware grabs the headlines, each risk highlighted in that poll is a symptom that could eventually lead to a ransomware attack, data leak or other security breaches.
As the threat evolves across multiple areas of risk, how should we address it? What are the strategic approaches we can take to tackle the complex security challenge?
Let me share with you some steps to consider.
Zero trust
The idea that we implicitly trust based on single authentication action is no longer appropriate. Zero trust aims to address this by continually checking access across multiple vectors such as user, location and device-state to build a detailed picture of security at all times on any given login attempt.
Strong Identity Security
As mentioned earlier identity is a crucial security battleground. Bad actors want your identity, because with it they not only gain access to your systems, they gain legitimate access. Ensuring we protect our identities, harden their security, and reduce exposure from risks posed by privileged accounts should all be priorities.
Be proactive
The rapid change in security threats means we cannot rely on static systems to maintain security. We need systems that can understand risky behaviour, quickly identify threats and help to mitigate them. Spotting unusual activity puts us in the strongest position to tackle data loss, ransomware, and a wide range of other malicious activities.
Overall Insight
Knowing what is going on in your organisation is critical in staying ahead of the security risk. As we have discussed, the security threat is multi-layered, as is our response. And while a multi-layered approach is vital it means we often have disparate systems dealing with risks. While this is no bad thing, it presents potential issues and the chance of missing significant risk indicators, therefore consolidating this information has become a major enterprise challenge.
This has seen a growth in SIEM and detection and response platforms that help to aggregate security information and to provide an overarching view. This broad view allows us to apply greater context and make better decisions based on the information presented.
Defend against ransomware and the causes
While ransomware remains top of the priority list for many, and with good reason, it is important to understand that ransomware on its own is not the problem and that It is the result of an exploit of other problems in your security stack. Hence the question, protect against ransomware or the causes? Of course, the answer is to do both, the best way to reduce the ransomware risk is to make sure you are tackling its causes.

